Digitisation of the world has induced various changes for the betterment of humankind. Now, almost everything can be monitored, controlled, traced and tracked when needed and when one has proper knowledge. With that, data has also become the most valuable asset for an individual and organisation.
But, given the intricate nature of the data and how it is interconnected, it is not always possible for one to realise one’s digital footprint. Nonetheless, this is now possible with the information system audit (IS audit) that allows one to have a proper data management system without compromising their security. Even in Nepal, from the past decades, slowly the information system audit has been coming into practice.
So, here are some basic things that you need to know about it.
What does an information system audit entail?

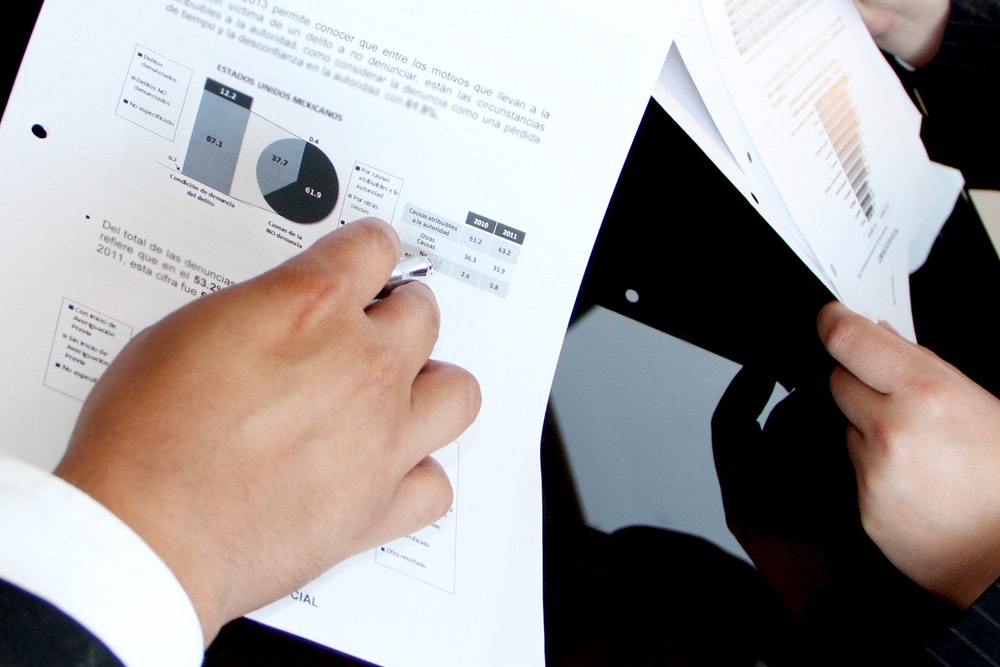
An information system audit is a means to monitor and appraise the management of information, their activities, their adopted system whether inside a big or small organisation. Monitoring of an organisation’s transaction, database management system, plans and policies as well as human resources fall under this audit approach.
Some of the basic forms of IS audit in practice are software/application audit, public key infrastructure (PKI) audit, database audit, and policy audit.
The IS auditors not only monitor and identify the errors within the organisations and their information system but also give suggestions in the decision-making process for the improvement of the business.
Why is it important?
Surprisingly, the idea for IS auditing was first made during the mid-1960s. Its technicalities were developed steadily, directly proportional to the advancement of modern technology.
In many countries including Nepal, the government has made it mandatory for certain categories of companies to perform the IS audit, since 2019. When an institution performs IS audit, it can measure its loopholes and weaknesses within its information system, identify possible sources of threats, assess information misuse and identify high-risk factors.
The main goal of IS audit is to help the organisation’s information system managers efficiently fulfil their tasks and responsibilities to obtain the organisation’s goals as well as improving proper decision-making and security of data and information. Tracing one’s information can even help in data recovery, in case any error has been made.
Organisations, big or small, have their data, user information and other in-house information. With the implementation of IS audit, an organisation can ensure confidentiality, integrity, availability, authority, authenticity, and non-repudiation of the information.
Who is authorised to conduct IS audit?

A certified IS auditor should be familiar with IT security and infrastructure, internal audit, data analysis and visualisation tools, security risk management, security testing, and auditing, computer security, analytical and critical thinking. They should be able to analyse, evaluate and sort organisational technical infrastructure to sort out the errors effectively with risk management and compliance.
Eminence Ways Pvt Ltd and Biz Serve IT Pvt Ltd are two government-authorised Nepali cybersecurity companies that are allowed to perform external IS audits and compliance tests. However, many other companies and individuals are also involved in the job after obtaining certifications such as CICA or Cisco.*
How often should companies perform it?

The IS audit evaluates the management controls of the information system. So, an internal audit is suggested to be implemented monthly or bi-annually depending on the organisation’s size and risks.
It is highly recommended that organisations perform at least one IS audit yearly.
Any external IS audit gives organisations the evaluation and opinion regarding the information security and about its compliance in accordance with the company’s policies, tasks, data preservation and implemented management control systems.
Legalities
IS audit regulations are guided by the Nepal Rastra Bank’s IT policy and IT Guidelines (2012).
According to the guidelines, an organisation should take the required measures to inform its employees, contractors, consultants aware of IS policy of the company and comply with it which can be done by proper employment information, employee agreements, policy awareness and its acknowledgements.
Also, they are obligated to conduct Risk Assessment periodically, at least once annually, within an agreement of technical operations that can greatly impact the business and reputation of the organization and act accordingly.
According to the guidelines, if the institutions do not have enough staff or expertise to conduct IS Audit, they can outsource it to an external professional provider.
* Update: The Nepal Telecommunications Authority on June 24, 2021, updated and made public a standing list (roster) of IS auditors and cloud auditors authorised to conduct the said tests as per the requirement of clauses 55 and 57(iv) of Cyber Security Byelaw, 2020. Click here to find out. Before that, only two companies were recognised for the task.